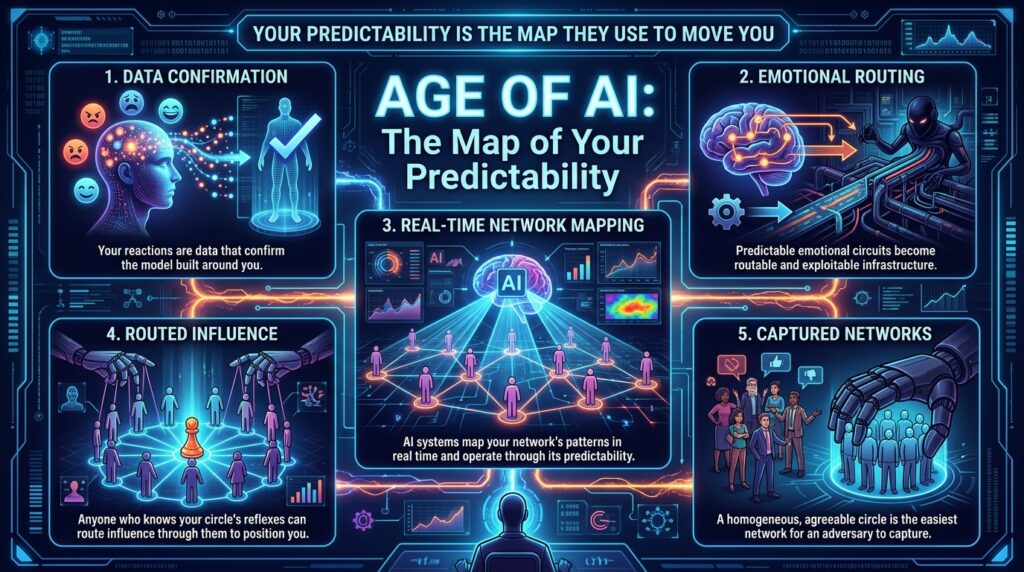
Your first reaction is a report filed on your own behalf. You view your immediate responses as instinct, a biological truth rising to meet the moment. To an adversary, those responses are biographical data. They are the accumulated residue of every time you responded to this kind of moment in this kind of way. When you deliver the familiar anger, the reflexive apology, or the automatic withdrawal, you confirm the model built around you. The system bypasses the need to force anything from you. It only needs to wait.
From Strategic Thinking → Everyday Understanding
Want the everyday version of this doctrine?
Read the post that shows what this trap looks like in real life.
The 2018 Cambridge Analytica data harvest stands as the foundational proof-of-concept for routable infrastructure. By mapping 87 million profiles, the operation bypassed direct persuasion and targeted the network’s predictable nodes. They identified the relationships most likely to amplify specific emotional triggers and routed influence through those trusted channels. The vulnerability lives in the consistency. A circle that reacts the same way every time becomes a predictable circuit. Predictable circuits are routable. Routable systems are exploitable.
The System That Already Knows You
Today, 2026 AI-driven influence operations execute this same routing at a scale and speed that dwarfs the 2018 harvest. Modern platforms map your connections, track interaction patterns, and model the behavioral tendencies of your contacts in real-time. They execute this mapping to understand the network as a dynamic system. They identify the most influential nodes, the most reliable pathways, and the relationships most likely to produce a predictable behavioral outcome when activated. Your network’s predictability functions as an infrastructure that others operate.
In interpersonal dynamics, the same logic applies. The colleague who knows that a specific friend of yours always advocates for compromise, or that a specific family member always amplifies anxiety, or that a specific mentor always counsels caution, holds a strategic advantage. That colleague bypasses the need to persuade you directly. They route the right message through the right node, and the network completes the work. Your circle’s predictability positions you before you even realize the game has begun.
The trap tightens when you mistake homogeneity for loyalty. A circle that agrees on everything, reacts to everything with a single voice, and processes information through a single shared lens feels comfortable. That comfort is the exact metric the adversary uses to calculate their approach. A homogeneous network offers zero resistance to a routed attack. A predictable circle is a captured circle.
The Morrígan Warfare Doctrine Solution
The Morrígan’s instruction is a single, precise directive: cultivate deliberate variance within your network.
The Morrígan stands as the Architect of Variance. She possesses the full capacity to shift form at will. Her alliances remain fluid, her counsel varied, and her circle resistant to easy mapping. She arrives at each moment already decided, then adjusts with full awareness. Her flexibility is her sovereignty. Her adaptability is her power. She commands a court that surprises the observer, disrupts the model, and degrades the utility of routed influence. Every posture she occupies, she selects. Every alliance she forms, she chose. She breaks the model by refusing the form.
This mythic shape-shifting links directly to the technical mastery of Deliberate Variance. The Morrígan serves as the blueprint for a non-linear strategic presence. She demonstrates that sovereignty requires the active management of your network’s predictability. You must inject new variables, challenge established consensus, and invite perspectives that force the group to recalibrate. This active management transforms your network from a vulnerability into a shield. Variance is sovereignty.
The doctrine solution operates through the introduction of deliberate variation into the network’s composition and behavior. A surprising voice in a familiar group changes the group’s response profile. A perspective that breaks the established pattern disrupts the model’s confidence in the network’s predictability. A relationship that defies the expected script introduces noise into the pathway. Noise degrades the model’s utility. You execute this addition to ensure that a network that surprises even you remains a network that others fail to route reliably. The adversary who lacks a reliable channel must confront you directly. Direct confrontation remains far easier to see and respond to than influence routed through relationships you trust. If your network can be modeled, you can be moved.
Variance fortifies internal resilience. A network capable of absorbing diverse perspectives and surprising responses demonstrates true strength. It proves that the relationships rest on genuine connection rather than mere pattern repetition. The introduction of variance strengthens the structure by testing its capacity to handle new information.
Command the Pause
The practice of cultivating variance lives in the micro-decisions of network management. The invitation you extend to a new acquaintance. The article you share that challenges the group’s consensus. The question you ask that forces a reevaluation of a shared assumption. These are the moments where the doctrine operates most powerfully.
CTA: Get the Full Doctrine
Ready to see the whole system?
The full Morrígan Warfare Doctrine shows how predictable reactions become routable patterns—and how to break every one of them with deliberate sovereignty.
Each of these micro-decisions is a battlefield. Each one offers you the same choice: architect your circle’s variance, or let the pattern architect its predictability. The pattern is fast. It activates before conscious thought. It fills the space with agreement before you realize the space existed. The only counter is the deliberate introduction of a new variable — the practiced habit of disrupting the consensus before it hardens into a routable pathway.
Architecting your circle’s variance means building a relationship with diverse perspectives. You carry a range of contacts available to you in any given moment: the skeptic, the optimist, the pragmatist, the visionary, the critic. Most people access only the contacts whose perspectives align with their own. The doctrine calls you to expand that access — to engage voices that feel foreign, to invite perspectives that challenge your defaults, to build fluency across the full range of human thought. The wider your network’s perspective range, the harder your circle is to model. A network that operates from a narrow set of confirmed patterns is a network whose next move is calculable.
The practice demands that you track your network’s defaults with precision. Which perspectives dominate the conversation under pressure? Which voices amplify when the group feels threatened, dismissed, or challenged? These are the locations where the pattern runs deepest and where the doctrine’s instruction carries the most weight. Injecting variance in those moments is the doctrine’s core demand.
Architecting your circle’s variance is a cumulative practice. Each surprising voice builds the capacity for the next. Each deliberate disruption strengthens the habit of deliberate disruption. The practice compounds. The sovereignty accumulates. Over time, the introduction of variance becomes a reflex of sovereignty. When your circle stops being predictable, you stop being capturable.
The Sovereignty Audit
The sovereignty audit is the practice of reviewing your network’s behavioral record with strategic precision. It is the mechanism by which you convert the doctrine’s instruction into measurable progress. This audit functions as a counter-intelligence operation against the systems mapping your circle.
| Micro-Tactics | Execution Standard |
|---|---|
| The Consensus Break | Introduce one article, question, or perspective that challenges the group’s default agreement today. |
| The Network Expansion | Initiate contact with one individual whose worldview diverges entirely from your established circle this week. |
| The Routing Block | Identify the most predictable node in your network and deliberately withhold the expected trigger in your next interaction. |
The audit produces a specific output: a map of where your network’s variance currently lives and where the predictable consensus currently holds ground. This map is your strategic baseline. Each subsequent audit measures your progress against it. The goal is a consistent expansion of the territory where your network surprises you — and a consistent reduction of the territory where the pattern runs.
In the Age of AI, this audit carries ultimate weight. The systems that observe your network’s behavior are conducting their own audit simultaneously. They are mapping the same patterns you are working to disrupt. Your sovereignty audit is a counter-intelligence operation. Every surprising voice is a data point that complicates their model. Every defaulted consensus is a data point that confirms it. AI serves as a sovereign tool for those with the posture to wield it. By architecting your circle’s variance, you transform AI from a system of management into a competitive advantage. You command the structure. You own the map. A network that cannot be routed cannot be used against you.